Build Effective Identity Management in Hybrid and Cloud Environments
Meet the Experts
By Craig Powers, Research Analyst, SAPinsider
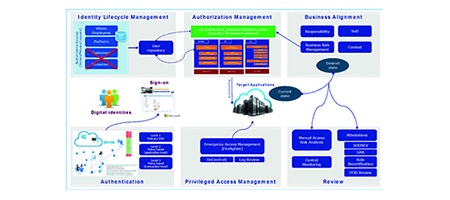
As more employees work remotely, and organizations shift to hybrid and cloud software and technology environments, identity management has become a more important piece of the access and security landscape. Critical assets no longer sit behind traditional firewalls, with employees accessing important corporate data from outside a single place of work. Automation can help companies more efficiently and effectively manage identities.
The Challenge of Automating Identity Management
“The first thing is to appreciate that enterprise IT environments are complex and constantly evolving. New types of identities – both human and machine – get added every day, making automation necessary. But many organizations have faltered because they have underestimated what it takes to automate,” says Amit Saha, CEO of Saviynt, which specializes in identity governance and administration.
Many companies are trying to automate much of the workflow around identity management, and to do that they need to have a robust set of processes that ensure clean sources of identity data coming from human capital management or contractor management systems, Saha explains.
That clean identity data is then used to give users access to SAP roles — which can be standardized or emergency access roles. However, this is not limited to the core SAP system. Applying access across non-SAP systems is important.
“Developing the right processes and instituting the right changes within your organization are critical,” says Saha. “Companies must be prepared to undertake that challenge and partner with an identity management vendor that can simplify these workflows.”
Strategies for Identity Management
Visibility is central to good identity management across hybrid environments. Organizations need to know who is using their systems — they could be an employee, an intern, or a contractor — and what access they have.
Once you have that visibility, the next step is to classify users and their access based on risk. Higher risk access may require more layers of approvals, while lower risk access could be automatically approved to lessen the burden on staff.
Finally, it is important to know what people are doing with the access they are given — are they doing what they are supposed to do, or are they performing something malicious? Are they at risk for ransomware? Do they have a compromised endpoint device?
“If they are displaying any malicious intent, or actually violating policies, it’s about clamping the breaks down on that person’s access,” says Saha. “How quickly can we react to threats, automate remediation, and trigger remediation across every system?”
The Goals of Automated Identity Management
When it comes to the results that his customers are looking to achieve with identity management, Saha says that the speed of getting access to a new user is important. Identity management automation should start from the first day a person joins a company, they should not be waiting for access to be granted.
Saviynt’s customers are also looking to improve their ability to identify and stop different attacks. They want to be able to look at how identity management is interacting across systems — SAP, Microsoft Azure, and Salesforce, for example. The goal is to reduce excessive permissions and identify violations — and provide evidence of that to external auditors.
Saha says that with that information at one’s fingertips, the time spent on audits can be reduced by as much as 40%.
How AI and Machine Learning Can Improve Identity Management
Saviynt has worked with companies such as BP, Western Digital, Mass Mutual, and Koch Industries to help them transform identity programs by leveraging machine learning and artificial intelligence (AI) to increase workflow efficiency, apply Zero Trust principles, and improve security posture. Machine learning and AI can be used to determine what is a sensitive or risky user or transaction and what is not.
Adding machine learning and AI helps customers focus initial identity management phases on critical aspects, such as compliance needs and the most sensitive transactions. For example, if a company is going through mergers and acquisitions, or divestiture, there could be information in its SAP and non-SAP systems that is deemed sensitive. Being able to identify the most important identity needs through machine learning and AI can help companies optimize their resources.
He adds that Saviynt customers have adopted an agile approach that delivers incremental improvements as part of the identity transformation program. This process allows stakeholders, such as SAP owners, end users, and IT owners, to regularly see value rather than wait until a long-term project concludes.
How Saviynt Approaches Identity Management
“Saviynt is focused on a tailored approach for identity management,” says Saha. Every company has a different set of roles that are important, and different technology landscapes with various levels of cloud adoption.
Risk insights are key to Saviynt’s strategy, capitalizing on security tools that many organizations already have in place, such as a cloud access security broker (CASB), endpoint security, and network security solutions. Combining all these risk elements and utilizing AI capabilities can help guide organizations on making better decisions faster.
What This Means for SAPinsiders
Good identity management requires people data integration. To know who is accessing your system, you need visibility to the right people data. This can be found in multiple places — including core human resources systems and wherever you are housing your contingent and contract labor information.
It’s not enough to know who is using your system, you need to know how they are using your system. The process of identity management does not end once the decision to give access or not is made. It is important to set up capabilities for checking if that user is behaving correctly. This should include automation to trigger governance and identity systems to potentially eliminate improper access.
Reduce audit time by unifying identity management across systems. Creating a unified solution to manage access across all assets allows enterprises the ability to gain insight into how user access is managed across your whole technology landscape. This means if a user abuses access in one system, they can quickly be blocked on other systems. That is good for company security, and it will also reduce audit time as that information can be easily accessed and shared with the auditor.